It’s been a while since I opined on matters I know little about…so I thought I would continue that tradition by putting out a few thoughts about all things cyber. No doubt you have all heard about cyber-xxxxx until you are becoming immune to the cries of “Danger Will Robinson.”
 And that is a real problem because cyber crime, cyber snooping, cyber intrusion, cyber war, and all manner of other things is perhaps the most significant challenge to the well-being of the good ole US of A in this century, IMHO. I’ve attended a series of meetings and had a couple of events in my personal life that have caused me to think a lot about this problem. But they way, I don’t claim ownership of any of these ideas. I have heard them in a variety of places from a variety of people. I just wrote them down in one place.
And that is a real problem because cyber crime, cyber snooping, cyber intrusion, cyber war, and all manner of other things is perhaps the most significant challenge to the well-being of the good ole US of A in this century, IMHO. I’ve attended a series of meetings and had a couple of events in my personal life that have caused me to think a lot about this problem. But they way, I don’t claim ownership of any of these ideas. I have heard them in a variety of places from a variety of people. I just wrote them down in one place.
Nothing chafes me more than getting my credit card rejected, and then finding out that my credit card company has detected the unauthorized use of my card and I must get a new one. That’s when I realize just what a poor job I have done in protecting myself….I even have a spreadsheet now with all the web sites that I have to visit to update my credit card number. It has web addresses, user names, account numbers and passwords all laid out so I can spend about two hours on line changing them all…..Am I the only one with this problem??? I’ve started trying to put everything on line through PayPal, but who’s to say that won’t be hacked next?
Think about all the bad things that have happened due to cyber crime in the last year or so…..Target gets hacked, the Joint Staff email system is fried, the Pentagon Food Court is penetrated, the OPM debacle. 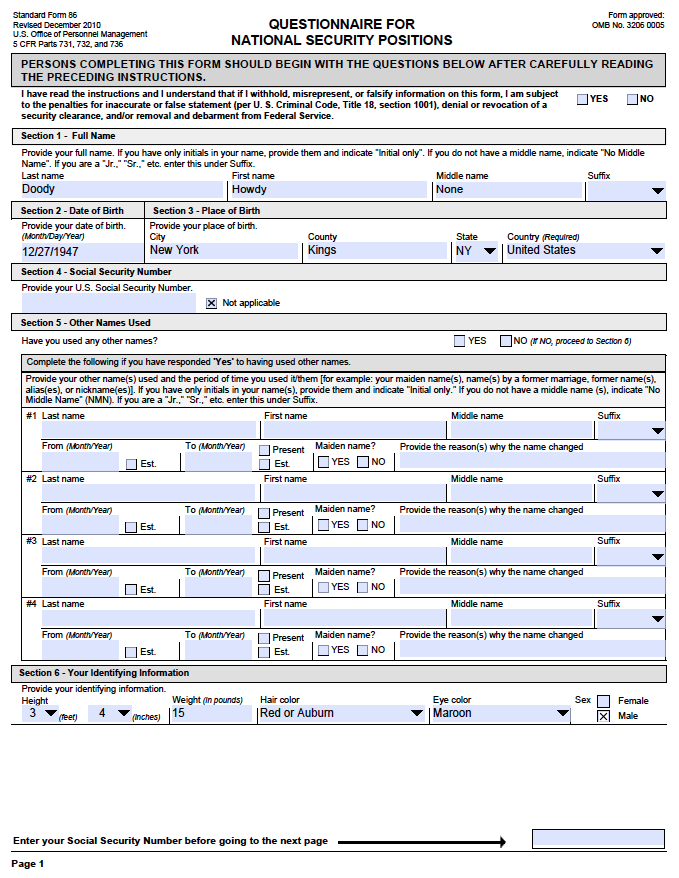 BTW I just got my ( less than timely) letter last week from OPM informing me that all the information on my SF86’s was compromised….that’s efficiency for you!!! (No wonder they got hacked if the timeliness of their notification is any indication of their expertise) How long has it been since we all knew about the OPM fandango???? And yet…..no one has gone to jail on the criminal side and no one has been fired or disciplined ….for any of those things. And I’ve got to say that in the case of OPM, it seems to me the cure is worse than the disease….Let me get this straight…..I get free monitoring for a couple of years and all I have to do is enter in all the personal information they couldn’t keep secure anyway…They want me to enter driver’s license number, bank account numbers, credit card numbers….What kind of idiot do they think I am? They gooned it up once……and most likely will goon it up again…There’s no way I’m putting all that info into anything that has anything to do with OPM or the US Government, for that matter…( Isn’t the lowest bidder providing most of the government’s security packages?). They should just ask the Chinese or the Russians for my info, since they apparently already have it………but I digress.
BTW I just got my ( less than timely) letter last week from OPM informing me that all the information on my SF86’s was compromised….that’s efficiency for you!!! (No wonder they got hacked if the timeliness of their notification is any indication of their expertise) How long has it been since we all knew about the OPM fandango???? And yet…..no one has gone to jail on the criminal side and no one has been fired or disciplined ….for any of those things. And I’ve got to say that in the case of OPM, it seems to me the cure is worse than the disease….Let me get this straight…..I get free monitoring for a couple of years and all I have to do is enter in all the personal information they couldn’t keep secure anyway…They want me to enter driver’s license number, bank account numbers, credit card numbers….What kind of idiot do they think I am? They gooned it up once……and most likely will goon it up again…There’s no way I’m putting all that info into anything that has anything to do with OPM or the US Government, for that matter…( Isn’t the lowest bidder providing most of the government’s security packages?). They should just ask the Chinese or the Russians for my info, since they apparently already have it………but I digress.
As I have been thinking about cyber security and listening to the experts over the past few months, it has dawned on me that this is a problem like no other we have ever encountered. And that means it’s going to require some very innovative and unconventional thinking to fix it (and thus the perfect reason why DoD shouldn’t be in charge). Moreover, this problem is much too serious to be given to the techies to manage. This is far too important to keep in the IT closets of government and corporate America. Management and leadership must know this stuff cold and be intimately involved every day, in every way. Why do I say that? Here are a few unique aspects to the problem:
- Everyone is an operator. Except for a few holdouts from America’s Greatest Generation, virtually everyone is slammin’ away at a keyboard or tip-tapping on a touch screen or talking to Siri(for those who are unable to get anyone else to talk to them). You don’t need a license, or any training, or have any awareness of just how badly you can screw things up to “operate” on the Internet. You all know people who shouldn’t be allowed on the Internet….the people who actually reply to the email from Mr. H. J. Spankle, Esq. from South Africa telling them that their long-lost cousin has left them a fortune. Or the ones who hit the “reply” button on the email from their bank telling them to update their user name and password……And yet they are all out there spending hours on-line, causing who knows how much damage. Their vote counts just as much as yours, by the way. This is why cyber experts will tell you that in most breaches, it’s not technology, but people at the root cause.
- There are no boundaries. There are no borders to control, no time zones, no hours of operation, no holidays, no boundaries of any type on the Internet. As a result, it’s not clear where jurisdictions begin and end. I suppose you could say that firewalls are a type of boundary, but even the best of firewalls eventually get penetrated. I was recently visiting NAS North Island in San Diego and went to the Mother of all Starbucks, located next to the carrier pier. I tried to use my smartphone app to pay for coffee, but was told they weren’t allowed to use that feature on the base because of the possibility that using the Starbucks Pay App might cause a cyber-intrusion in the base network…Huh? If that’s the case on NAS North Island, why isn’t that the case at any Starbuck’s. They don’t even use the Navy network and yet the Navy is worried about intrusion. Can that be true? Do the folks making those decisions really know what they are doing??? I hope so, but it doesn’t make sense to me. This type of mentality reminds me of the old saying in Naval Aviation, ” If safety was paramount, we would never fly!”
- No one is in control. This relates to the no boundaries problem. Since there are no boundaries, it’s not clear who is in charge. Of course, there are several organizations that may exercise some moderate influence, like the Internet Corporation for Assigned Names and Numbers (ICANN) or maybe some of the companies maintaining Authoritative Name Servers (the keeper of the “phonebook” for domains like .com, .net, .org, etc) Until about 1999, a company known as Network Solutions,Inc. did this function, but now several entities claim this responsibility, along with organizations for domains like .biz and .edu. The United Nations has been monkeying around with Internet Governance as well, claiming that they don’t want the US in charge (BS IMHO) but in the end there is no single “belly button” in charge.
- There in no difference between military, government and civilian operations. Everyone is in the same boat. This becomes a real problem after a hacking event when trying to attribute the attack to someone or something. Was it a hostile act by an opposing military power or was it a criminal act by some organized crime actor, or was it a terrorist act by a radical group, or was it just a random act of boredom by a “hackivist” wasting time between Minecraft games? Who knows? It all looks the same. This is a fundamental problem in determining what type of response is appropriate for any given attack. I have no doubt the US has the capability to “smoke check” every single computer in North Korea….or even turn my own laptop into a time bomb fueled by a “Phaser Overload” in my lithium battery pack, but to what end? Is it our responsibility to be the “Net Police”? Is it DoD, DHS, FBI, FCC, Radio Shack???? I just don’t know (and apparently neither does any of our leadership).
- All share in the risk. Just look at the Target incident. Even though I might have been a completely hygienic internet user with impeccable security habits, all I needed to do was buy a lightbulb from Target using a credit card and BINGO….I’m hacked!! And think about the problem of someone else using your computer for whatever reason…all they need to do is click on one spam message and you are hacked. In fact, it takes just one ne’er-do-well on your vastly secure network to plug in one thumb drive, and you are hacked. You are at risk, even if you chose not to play the game. This has huge implications. BTW, do you all have the new credit cards with the chip that is supposed to enhance security? You know, the one that doesn’t work in any of the credit card readers?????? As far as I can tell it’s still swipe, swipe, swipe your personal information away!!!!!!
- Cyber-Health is nonexistent in the masses. Probably an overstatement, but the point is that even very well educated folks are constantly falling prey to all sorts of scams, phishing schemes and electronic theft. Think about the little device that criminal stick to the ATM card slot that copies all your ATM card info. Or what about the scanners that can cue your smart phone to dump its address book (now we need metal card holders to prevent intrusion, a la the new Pentagon Badge Holders?). So my contention is that the vast majority of internet “operators” pay about as much attention to cyber-hygiene as they do about the dangers of texting and driving…..Once again, it only takes one to spoil the whole barrel and there are plenty of rotten apples running around out there.
So there are just a few reasons why cyber-related problems are unlike any we have tackled before. No great revelations here and sadly no solutions. But I contend that to get to the solution, we must first understand the problem we are fixing. I don’t think we are anywhere near understanding the extent, nature or consequences of living in a world where everything is connected. To my way of thinking, we have too much of a good thing and that can be bad thing. I am reminded of a discussion I once had with a prospective bridegroom when I was a marriage mentor. We were talking about the special relationship between married couples….no secrets, everything open and above board…Then I remembered that sometimes openness and honesty may not always be the best policy when it comes to marriage….I made that mistake early on in our marriage…..I recall coming home just weeks into our wedded life and passing on the blueberry pie the lovely Mrs. Crenshaw has spent many hours preparing (after attending classes all day). “Just so you know, I don’t like blueberry pie,” I said. Some four-two years later I regret that moment of honesty every day!!!!!!!!!!

